When doing PKI audits and also when troubleshooting autoenrollment I want to see if there are multiple Group Policies that configure contradictory PKI settings.
Instead of manually going through all GPOs I wrote a PowerShell script that lists all GPOs that have PKI-settings in them, and also singles out those that configure autoenrollment.
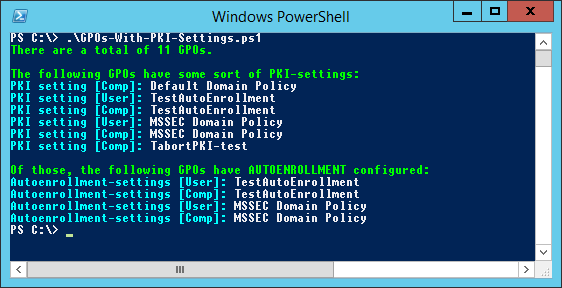
Here is a sample output:
As you can see I look in both Computer and User scope of the GPOs.
The script utilizes the commands Get-GPO and Get-GPOReport, so you need to run the script on a computer that has the Group Policy Management feature installed (like a DC) or a computer with the Remote Server Administration Tools installed.
As always, there is room for improvement. Besides error management, perhaps showing the actual settings and also where the GPOs are currently linked. Feel free to improve it, and let me know if I can reshare it.
You can view and download the PowerShell script here:
https://1drv.ms/u/s!ApDVTW2lda1rtekXQkWvT-SJTQYlvA
Standard Disclaimer: I am NOT a professional coder. I am not responsible for what this script does. Do a code audit and testing in test environment if you run it in a sensitive environment.
Please leave any feedback you have as a comment to this post.

I knew we had several GPOs configuring certificate autoenrollment, but I need to find out which one. Your tool did the job. Thanks a ton!
Thanks for the feedback, glad it helped!